Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 405
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 405
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 405
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 408
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 408
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 408
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 469
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 497
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 433
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 433
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 451
Warning: Trying to access array offset on null in /app/wordpress/wp-content/plugins/fusion-builder/shortcodes/fusion-toggle.php on line 451
UWB Sniffer Installation
Packet Analyzer For 802.15.4a UWBchnology
Packet Analyzer For 802.15.4a UWBchnology
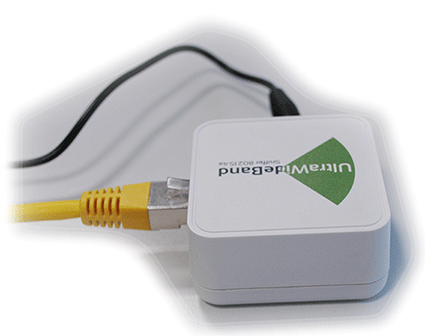
1) Hook up cables to UWB Sniffer
2) Setting TCP/IP at the host side
| Parameter | Value |
| DHCP server | OFF |
| Filter 802.15.4 frames with bad CRC | OFF |
| IP address | 10.10.10.2 |
| Network mask | 255.255.255.0 |
| Gateway address | 10.10.10.1 |
| Remote Host IP address | 10.10.10.1 |
| Remote Host port | 17754 |

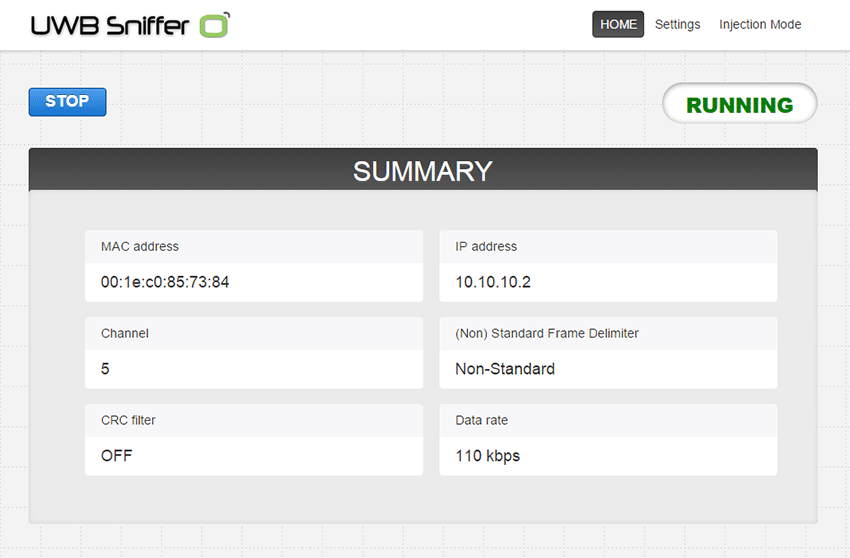
3) Connect to the UWB Sniffer homepage
1) Wireshark installation
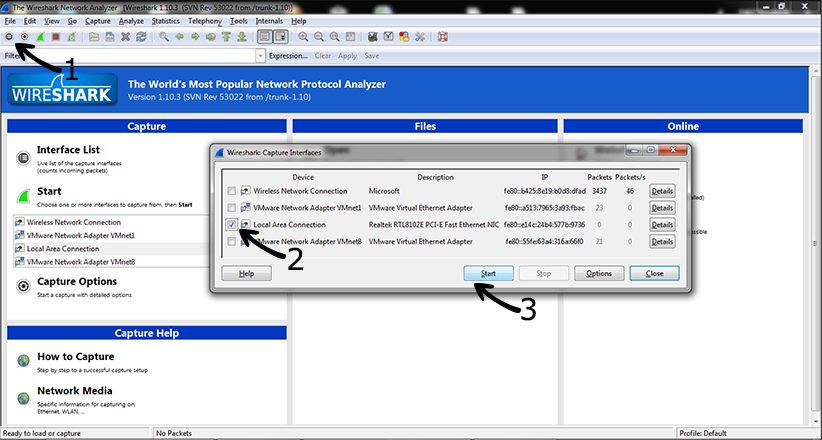
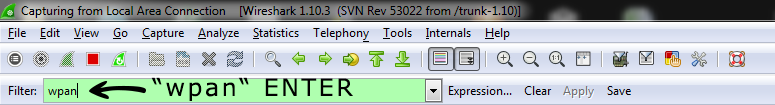
2) Start Wireshark capture
Wireshark implicitly shows all frames from wired and wireless networks delivered to the selected interface. Therefore, it is useful to apply 802.15.4 filter which is referred as “wpan”.
3) Start UWB Sniffer

4) Let’s sniff some communication
Adjusting Wireshark for 802.15.4 networks
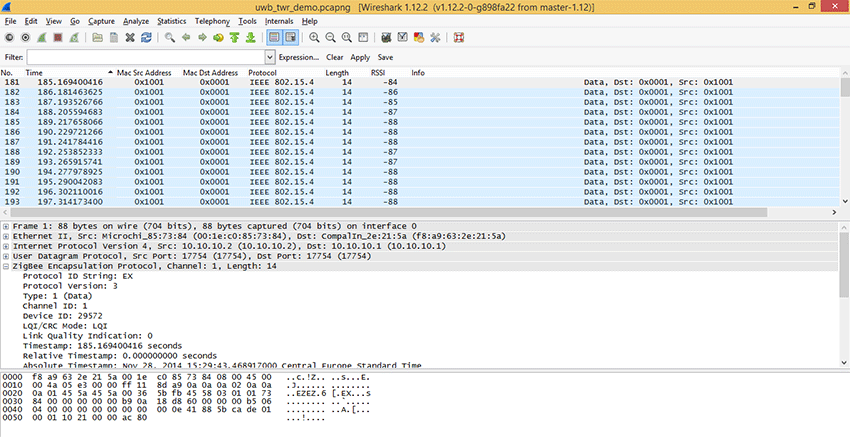
In the part two you have ended with some data captured and delivered to Wirehark. You may download the sample file uwb_twr_demo.1) Wireshark columns
Wireshark has default columns settings for wired Ethernet network, see picture below.
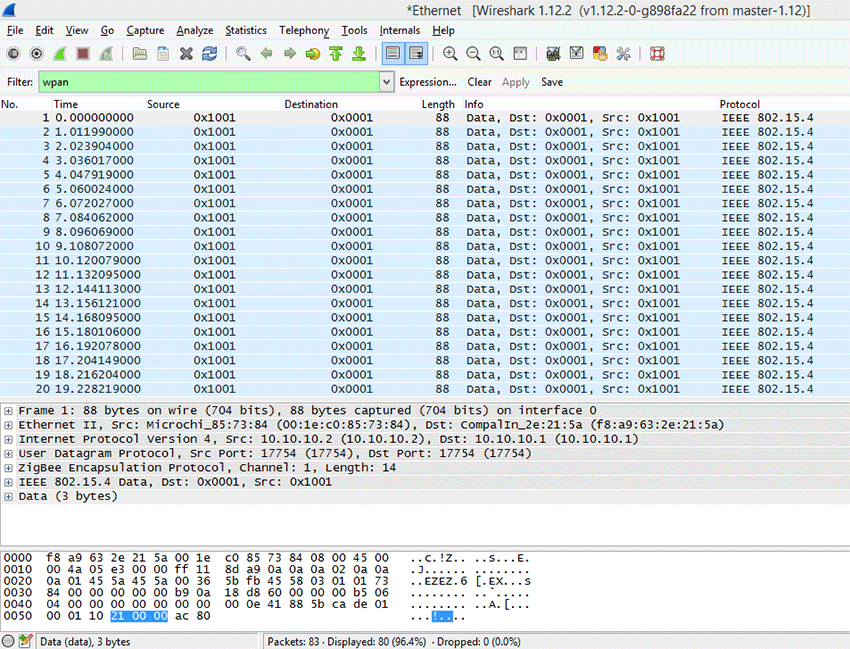
Columns are defined for the default Wireshark profile as follows:
| Column name | Description |
| No. | Frame number counted from the start of capture in Wireshark. This is NOT number of a frame received from UWB Sniffer. It includes all packets (wired&wireless) delivered to the host’s ethernet interface |
| Time | Ethernet timestamp of the frame assigned by the operating system. This is NOT precise timestamp from UWB Sniffer. |
| Source | Source Address |
| Destination | Destination Address |
| Protocol | Protocol |
| Length | Length of entire Ethernet frame including transportation overhead. This is NOT length of 802.15.4 frame |
| Info | Protocol details |
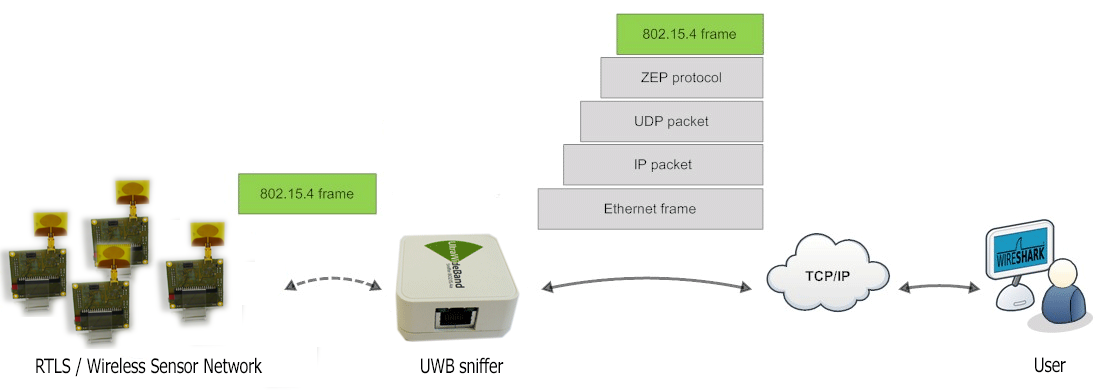
From the table above it is obvious the default column settings are not associated with 802.15.4. Therefore, user can adjust them to the 802.15.4 frame info. Let’s refresh the encapsulation scheme for each 802.15.4 frame delivered to the host (see picture below). While the grey colored protocols are used only to transport the 802.15.4 frame through a network infrastructure, the ZEP – Zigbee Encapsulated Protocol carries all the important information such as sequence number, timestamp or channel number related to the every 802.15.4 captured by the UWB Sniffer device.
2) Install ZEPv3 plugin
Although, Wireshark natively contains ZEP protocol v2, we have developed ZEPv3 which is backwards compatible. It brings additional information related to band, channel page and precise timestamp information.
In case that additional information are not interesting for you, you may skip installation of this plugin.
- Download ZEPv3 plugin here: Win_x86, Win_64
- Extract and copy plugin to the Wireshark plugin folder.
Windowsc:\Program Files\Wireshark\plugins\1.x.x\,
Linux/usr/local/lib/wireshark/plugins/1.x.x/. - Start Wireshark. menu Analyze -> Enabled Protocols (CTRL+SHIFT+E)
- Uncheck ZEP, check ZEPv3
- Apply, OK.
- If frames are not decoded with ZEPv3 go to menu Analyze -> Decode as -> ZEPv3 -> Apply, OK.
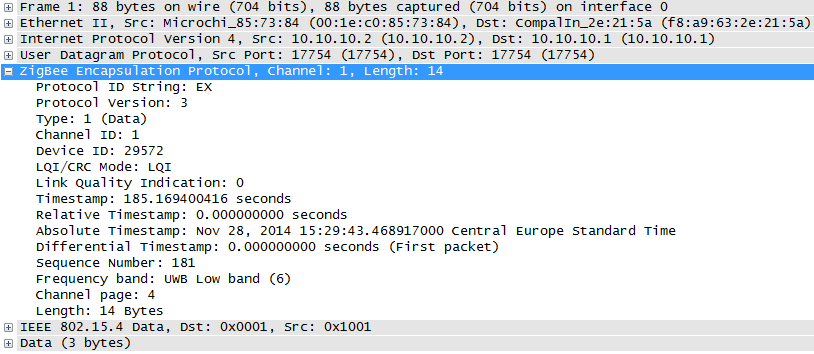
ZEPv3 contains fields depicted in picture below:
| Zepv3 Field | description |
| zepv3.version | zep version |
| zepv3.type | type of packet |
| zepv3.channel_id | channel number |
| zepv3.device_id | unique ID of the sniffer, based on MAC address |
| zepv3_lqi_mode | LQI/CRC either LQI is send to Wireshark or CRC value |
| zepv3.lqi | LQI value, not used in UWB Sniffer |
| zepv3.time | Time elapsed since sniffing was started at UWB Sniffer |
| zepv3.reltime | Relative time since sniffing was started at UWB Sniffer |
| zepv3.abstime | Absolute time converted to host timezone |
| zepv3.difftime | Differential time among packets |
| zepv3.seqno | Sequence number of packet send from UWB Sniffer |
| zepv3.band | IEEE 802.15.4 frequency band |
| zepv3.chanpage | IEEE 802.15.4 channel page |
| zepv3.length | IEEE 802.15.4 frame length |
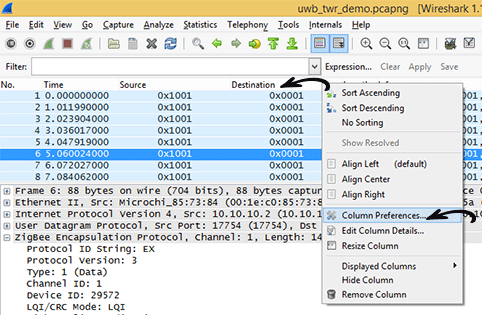
3) Adjusting Wireshark columns to 802.15.4 frame
Adjusting columns procedure:
- Right click on the columns header
- Select Column Preferences
- Adjust columns to 802.15.4
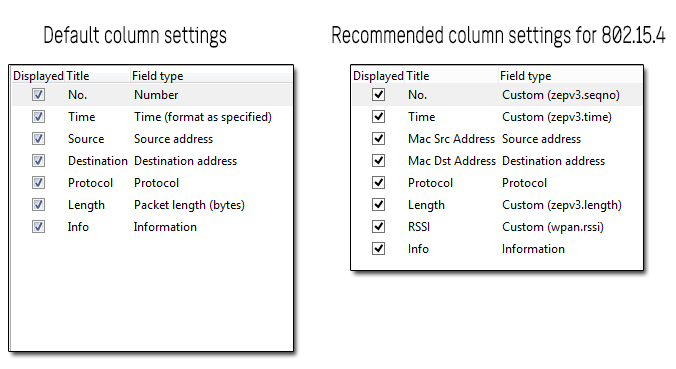
Adjusted Wireshark columns should seems like this:
Further reading
You may continue to read about UWB Sniffer Configuration.